Claude Mythos: Industrialization, Not Revolution
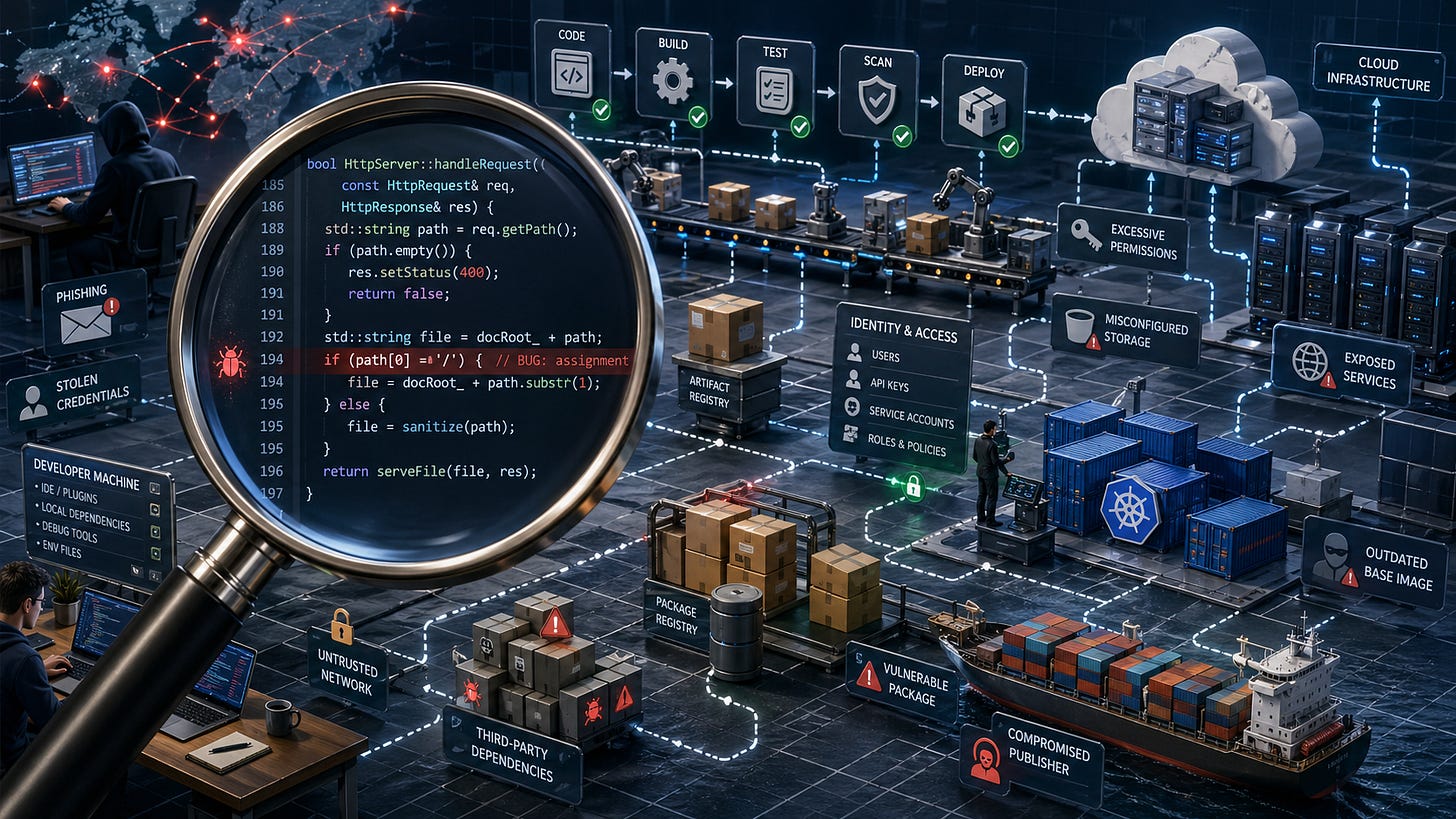
AI source-code auditing changes one slice of the cybersecurity surface; supply chains, attacker timing, and jurisdictional access are the rest of the picture.
Three weeks ago Anthropic launched Claude Mythos, a frontier model whose cybersecurity capabilities — discovering vulnerabilities, building working exploits, chaining them into multi-step attacks — sit materially above prior frontier models. The UK AI Security Institute (AISI) confirmed the step-up. Mozilla’s Firefox 150 release shipped engineering work at a scale Mozilla had not previously published in a single advisory. The defensive contribution on the slice of the cybersecurity surface that source-code AI auditing addresses is real.
The framing layered on top of that contribution has run ahead of it. Mozilla’s blog headlines 271 vulnerabilities for Firefox 150 while explicitly crediting Claude on three of forty-one Common Vulnerabilities and Exposures (CVE) entries. OpenAI’s “over 3,000 critical and high fixed vulnerabilities” claim from April 14 escalated to “11,353 critical and high-severity issues” by late April — a four-times jump in two weeks, with the counting unit quietly shifting from fixed to identified. These are competitive scoreboards, not engineering disclosures. The capability is real; the scoreboards are real; they are not the same thing.
The topic is technically dense and structurally tied to multiple strategic surfaces — defensive economics, supply-chain integrity, jurisdictional access, sovereign capability — none of which resolves to a single narrative. Announcements read as engineering disclosures but operate as marketing claims; separating the two requires working through each surface independently. I wrote a ~40-A4-page primary-source-anchored monograph on that basis. This post is the synthesis; the article is the work behind it, downloadable at the end of this summary.
The synthesis is a three-thread judgment.
First, Mythos is the industrialization of known-class vulnerability discovery, not a new category of capability. Mozilla itself reports that Mythos has not surfaced bugs an elite human researcher could not in principle have found. The change is in throughput and delivery mechanism — elite-style reasoning, machine-scaled, available with relatively little bespoke scaffolding. That is significant, certainly welcome, but it is not a paradigm shift.
Second, supply chain is the dominant blind spot in any defensive posture centered on source-code AI auditing. Eleven high-profile supply-chain compromises were examined, from SolarWinds (2020) through the March 2026 Trivy / aquasecurity case. None would have been prevented by AI-assisted review of legitimate downstream consumer code, because the malicious change typically did not live in the source.
The volume signal aligns with the case record. Sonatype’s 2026 State of the Software Supply Chain records 454,648 new malicious open-source packages discovered in 2025 alone — a 75 percent year-over-year rise.
In contrast, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) Known Exploited Vulnerabilities catalog, the public registry of confirmed in-the-wild CVE exploitation, grew by 31 percent year-over-year in the same window.
The supply-chain attacker surface is expanding at more than twice the rate of the catalogued CVE-exploitation surface — a structural comparison rather than a head-to-head one, since the two metrics measure different slices. Per-incident blast radius reinforces the point: a single supply-chain compromise can affect tens or hundreds of thousands of downstream consumers (SolarWinds: 18,000; tj-actions: ~23,000 GitHub repositories; IndonesianFoods: 169,538 packages; Polyfill.io: 384,773 hosts). A memory-safety CVE typically affects users of the patched product - though the impact can be large with operating systems, browsers, or media players.
Third, access to Mythos-class capability is structured along jurisdictional lines that produce competition-distortion effects independent of technical capability. The named Glasswing partner roster is American — ten US-headquartered firms plus the Linux Foundation. The European Commission is in active discussions but does not have access. The UK does, probably along the same intelligence-sharing geography that has governed transatlantic security cooperation for decades, or because AISI has no equivalent in other EU countries in terms of technical capabilities.
A coherent European chorus has formed on the public record. France’s CIANum, Germany’s BSI, and the Bundesbank have each framed the asymmetry as a sovereignty or competitive-distortion concern. The argument is no longer Franco-French.
For European software companies in particular, the procurement-defensible question changes. A buyer evaluating two functionally equivalent network or security appliances in 2026 now has a defensible reason to prefer the vendor whose product was Glasswing-audited — not because of any belief about whether Mythos found anything load-bearing, but because one vendor was audited at frontier-AI capability and the other was not.
For decision-makers, the three threads translate into specific moves.
If you are a software vendor CEO whose competitive segments overlap with the named Glasswing roster: audit the procurement-defensibility exposure on a 12-24 month horizon. Position around quality, operational discipline, and externally-verifiable build-pipeline integrity rather than around frontier-AI access equivalence — the access asymmetry is unlikely to close on your timeline.
If you are a CEO, CPO, CTO or CISO at an organization outside the Glasswing roster: deploy AI-assisted code review on the highest-risk components first (authentication, session management, payment flows, file upload, deserialization paths) using whichever tier of frontier-model access is commercially available; instrument the triage pipeline before scaling discovery; pin all CI/CD action references to immutable commit crypted signatures (the Trivy and tj-actions lessons); audit dependency-update workflows for trusted-publishing posture.
If you are a board director or PE partner: the access-asymmetry structure is a 12-24 month consideration for 2026 software-sector strategy and acquisitions. Treat it the same way you treat any regulatory or supply-chain dependency that is structurally asymmetric across jurisdictions — a category of risk to factor into investment theses, not a precise pricing model the public record can yet support.
Across all three: extend governance attention beyond “do we have AI source-code auditing” to also include “do we have build-pipeline integrity controls deployed, default-on, enforced, and externally verifiable” — the controls are complements, not alternatives. Invest in the sovereign and operational levers that reduce jurisdictional access exposure while the asymmetry window is open — its resolution, whether through replication or entrenchment, is a 12-24 month question.
The cybersecurity contest has entered a new phase. Frontier-AI cyber capability is real, dual-use, and proliferating on a vendor-forecast timeline measured in twelve to twenty-four months. The right response is neither dramatic-shift rhetoric nor business-as-usual complacency. It is operational discipline applied to the three threads — capability calibration, supply-chain integrity, jurisdictional posture — at once. None alone is sufficient.
To be clear: invest in cybersecurity, now, and substantially. No vendor can afford a reputation hit from insufficient cybersecurity. As Thorbecke put it: ‘Trust arrives on foot and leaves on horseback’ (Vertrouwen komt te voet en gaat te paard, Johan Thorbecke, 1798–1872).
The judgment compresses to one operational sentence:
Mythos changes the economics of finding. It does not, by itself, change the economics of fixing, shipping, proving, governing, or accessing defensive capability.
The full monograph — primary-source-anchored, with a reference list, definitions, cross-jurisdictional press coverage, and a CO2-footprint calculation — is downloadable below. Four reading paths inside the PDF: end-to-end, skim for senior tech executives, technical-cyber, decision-maker.
Use the PDF to print; the ePub format may be easier on a tablet.
This analysis is free and will stay that way — access to evidence-grounded security thinking should not depend on a subscription fee. A subscription supports the work.
By Mathias Przybylowicz, Founder & Principal, Boxing Day Consulting · May 2026 Boxing Day Consulting — helps software companies overcome strategic and technical obstacles to achieve profitable growth.